…for now, that is. My previous posts were: DRM CD's are uncool, More on the DRM CD case, the great DRM aha!
On October 7th, I followed the instructions posted at the CDFreaks Club to remove Macrovision CDS-300 drivers. This consists of finding the file sdcplh.sys on your Windows partition/drive, deleting it, and restarting Windows. Boom. It worked. Marvelously. I also decided to disable Autorun on my optical drive, but it turns out that for all my knowledge, I didn't know how. Lol. Annoyances.org readily gave the solution. Like many things in Windows, it was in the Registry, but TweakUI handled it easily. So anyway, I could rip tracks fine now, no scrambled audio effect. Great! I tested it out by ripping the first and last tracks. No problems detected, MP3's played fine. I'm pretty sure this only affects Windows, so if you use Mac or Linux, rest easy. It seems kind of stupid for me to get suckered in like that. Oh well, now I know.
removing CDS-300
So, here's a step by step on how to get rid of the CDS-300 protection (How do you know it's CDS-300? There is a folder named CDS300 on the disc. Simple as that):
- Start Menu > Search
- If needed, click to search All files and folders
- Type in sdcplh.sys and then press Search
- Once it has been found, right click it and select Delete and select Yes if you are asked for confirmation
- Restart your computer once the file has been deleted
- Once you're back, enjoy unscrambled ripping of your CD!
Thanks to CDFreaks (hyqwn) and Alex Halderman and Edward Felten.
And if you ever insert that CD into a Windows computer again, I recommend holding down Shift whilst you do (i.e. press down before you put the disc in, let up a few seconds after the CD tray has closed or, in the case of a slot loader, you've inserted the disc) so that the program will not Autorun.
Also of note, there is an Uninstall.exe on the disc. I'm not sure if this would actually remove the driver (sdcplh.sys), but it does at least set the "agreement" status on the disc's autorunning up to "not agreed."
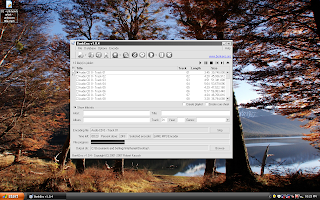
Here are some pics… before and after removing sdcplh.sys

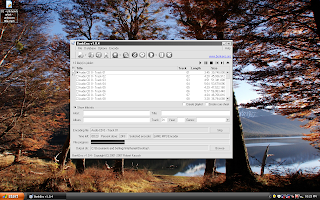
successful ripping!
There are also two other protections schemes I found out about during my research, MediaMax and XCP. I actually thought I had XCP on my CD, but it turned out to be Macrovision's CDS-300. So, I actually learned a fair bit about XCP and MediaMax. Much information can be found in Alex Halderman and Edward Felten's whitepaper. XCP, which only works on Windows, installs a rootkit on your system, which malware can and has taken advantage of. MediaMax, which works on Window and Mac (though the Mac version actually requires the user to start the installer), if Autorun is enabled (and it is by default), actually does automatically install software on your computer without notifying or asking you. Furthermore, MediaMax also opens up a security hole, as described in the whitepaper.
removing XCP
I've never actually encountered XCP (though I thought I had), but I'll list some instructions that I think would work to get rid of it, based on information I've gleaned from the internet. I am told that if the disc uses XCP protection, you'll see a file on it called VERSION.DAT (you might just see VERSION, depending on your Windows settings)
- open Run (Start Menu > Run or in Vista, just type in the search box)
- type cmd /k sc delete $sys$aries and press Enter
- restart your computer
- open Command Prompt (Start Menu > All Programs/Programs > Accessories > Command Prompt)
- type cd \ and press Enter
- type del $sys$*.* /s
- wait until it's done (it will have a list of deleted files and then finally display the prompt C:\>)
- restart your computer (I don't know if it's really necessary, but it's not a bad idea)
- You're done; I do recommend downloading CCleaner to clean up your Registry, though. Just open up CCleaner, click the Registry button on the left, and click Scan for Issues. Once the scan is done, click Fix selected issues… when it asks you if you want to backup changes to the registry, just click yes and save it in My Documents or somewhere else convenient. That way, you can just double click the file to reverse your changes if your computer starts acting wacky after this (assuming the Registry cleanup somehow created a problem that made things act wacky).
Thanks to Black and White Incorporated for the information.
removing MediaMax
The other big CD protection software is MediaMax. Halderman and Felten kindly explained how to remove the Windows version.
- open Command Prompt (Start Menu > All Programs/Programs > Accessories > Command Prompt)
- type sc stop sbcphid and press Enter
- type del %windir%\system32\drivers\sbcphid.sys and press Enter
In the future, always hold down the Shift key like I described earlier, if you put the disc in a Windows computer, because the software on the disc WILL install stuff without your consent. Unless you have Autorun turned off.
Regarding the Mac OS X version of MediaMax: I don't know too much about it, but I did find out that OS X does have an autorun feature (called 'autostart', I am told) that can start the process, but it still needs your permission to install the software. Don't give it that permission. Deny and rip away! If you do install it… I'm afraid I don't know how to remove it. Good luck if you try, and please share any findings with the community.
Well, that's it for now. Hope you have fun avoiding DRM.